By Max Amuchie | The Sunday Stew
Nigeria’s decoupling is not random — it is engineered. The state wears the mask of authority while its rivals wield the substance of power. In the vacuum, a rival order rises: taxing, renaming, and ruling with a clarity the state can no longer muster.
Part 1 named the condition. This second movement explains its mechanics.
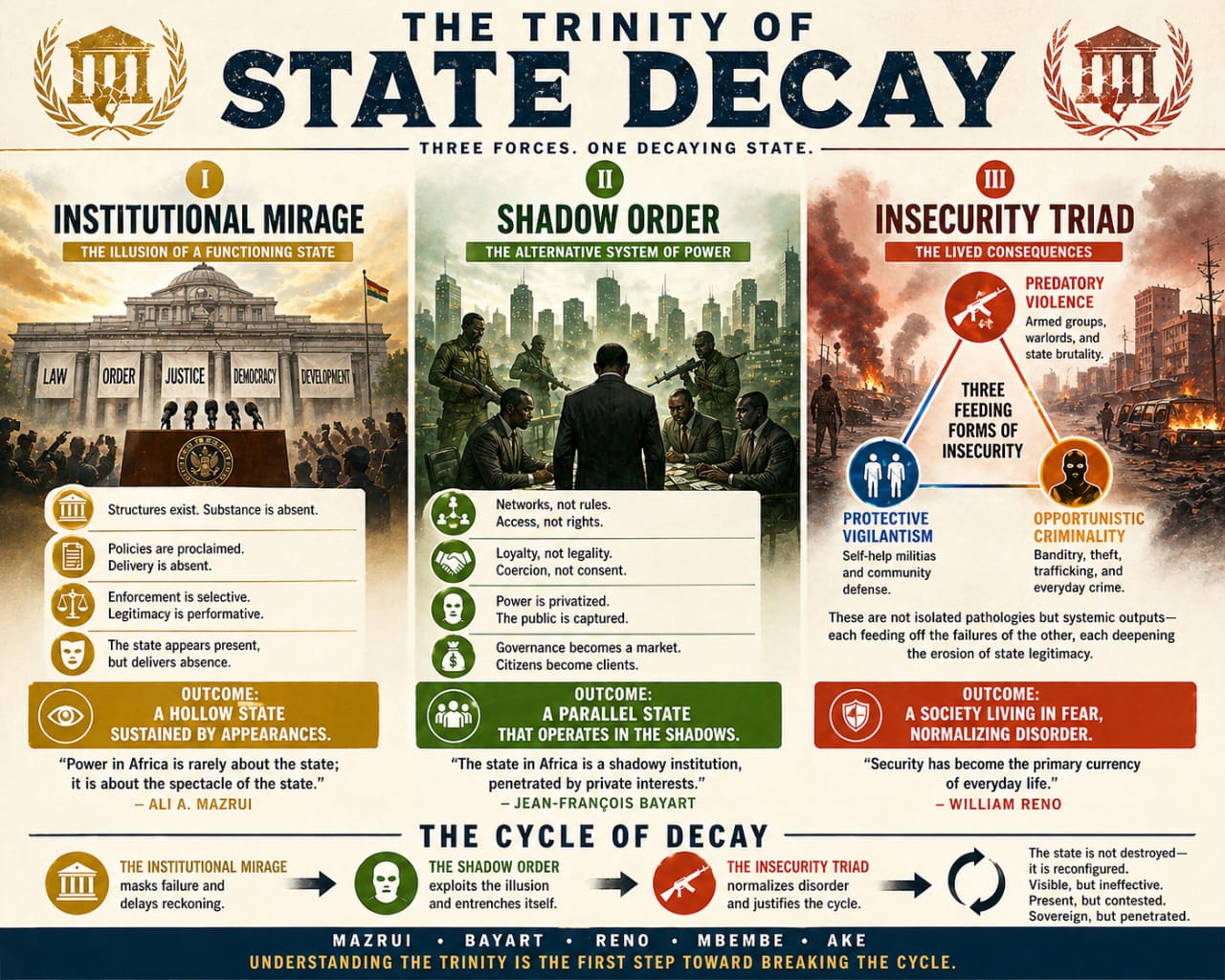
If the Institutional Mirage performs authority and the Shadow Order exercises it, then the question is no longer whether the state is weakening, but how that weakening is organised, sustained, and reproduced.
The answer lies in the Insecurity Triad — not as a collection of crimes, but as an operational system of governance that emerges in the interstices of state withdrawal.
What appears as disorder is structure. What appears as fragmentation is system. What appears as crisis is reproduction.
At the centre of this reproduction is a loop the state does not merely fail to break — but increasingly inhabits as its own mode of survival.
The Structural Interaction: Mirage, Shadow, and the Production of Void
The Institutional Mirage and the Shadow Order are not parallel formations. They are locked in a causal circuit — a self-reinforcing loop sustained by the Insecurity Triad.
The sequence is precise, not accidental.
The Mirage creates the vacuum.
By performing governance without delivering it — convening committees instead of enforcing authority, issuing declarations instead of securing territory, maintaining symbolic centrality while withdrawing from operational peripheries — the Institutional Mirage produces spaces where sovereignty exists in form but not in force.
These are not empty spaces. They are functional voids: zones where authority is declared but not operational, where legality exists but enforceability does not, where the state is present as narrative but absent as structure.
In these voids, legitimacy becomes unanchored from enforcement.
The Shadow does not enter these spaces as disruption.
It enters as replacement infrastructure.
It fills the vacuum through the Insecurity Triad:
Money — ransom economies that convert insecurity into revenue;
Land — territorial governance through coercive taxation and control;
Mind — ideological capture that replaces civic legitimacy with alternative authority systems.
The Triad is not incidental. It is not criminal residue. It is administrative architecture without formal recognition.
Together, these three logics form a rival system of governance that requires no elections, no constitutional validation, no external recognition. It requires only the sustained absence of enforceable state presence.
Constitutional Erasure: The Shadow’s Sovereign Inscription
The functional void produced by the Mirage is not passive; it is actively inscribed by rival authority. What Part 1 established empirically — the renaming of villages, the hoisting of rival flags, and the symbolic reordering of territory — now becomes analytically central as constitutional erasure within the Insecurity Triad loop.
Fanon’s insight is decisive here. To rename is to unmake — to dissolve one sovereign order and inscribe another in its place. The gun secures territory; the name governs it. Constitutional erasure is therefore not adjacent to governance. It is governance in its rival form — counter-constitutional inscription of authority.
Its significance lies in how it restructures perception and compliance. Once a community is renamed, the former constitutional designation becomes politically fragile. To invoke the state’s authority is to invoke an order that cannot enforce itself; to invoke the Shadow’s authority is to invoke one that can. The choice is no longer between legality and illegality, but between enforceable and unenforceable reality.
Constitutional erasure thus converts the Mirage’s vacancy into the Shadow’s jurisdiction. It transforms spatial absence into administrative capture, making subsequent compliance transfer structurally inevitable. The population is not simply governed differently; it is repositioned outside the state’s effective map of enforceability.
The Shadow does not request allegiance. It inscribes it through territorial naming itself.
Compliance Transfer: The Silent Relocation of Authority
As the Shadow consolidates control within functional voids, a second-order transformation occurs: compliance begins to migrate.
This is not ideological conversion. It is practical adaptation.
Populations shift allegiance along lines of enforceability rather than legality:
•taxes are paid to those who can enforce extraction;
•disputes are resolved by those who can enforce outcomes;
•rules are obeyed where consequences are immediate.
What emerges is not rebellion against the state, but rational substitution of authority under conditions of asymmetry.
Each act of compliance transferred is also an act of state erosion — not because the state disappears, but because its authority becomes non-competitive in lived reality.
At this stage, sovereignty is no longer monopolised. It is distributed according to functional capacity.
Dependency Turn: When the State Requires the Shadow
The loop reaches structural maturity when the state begins to adapt to its own displacement.
This is the most critical transition in the entire system.
The state does not confront the Shadow Order as an external adversary alone. It increasingly engages it as an informal stabiliser of governability.
This produces what can be described as Promotional Negotiation — the practice of purchasing temporary stability from a rival authority structure through ransom logic, informal settlements, or negotiated withdrawals.
This is not strategy. It is systemic dependency.
Every negotiation produces three systemic effects:
•It monetises insecurity by validating abduction economies;
•It territorialises Shadow authority by recognising de facto control;
•It legitimises the Shadow as a negotiating sovereign rather than a residual actor.
The paradox is complete: the state stabilises instability by financing its reproduction.
At this point, the Institutional Mirage is no longer merely performing sovereignty.
It is renting functional access to sovereignty from its own rival system.
Theoretical Architecture
The Trinity of State Decay is grounded in a layered theoretical architecture that explains the formation, operation, and persistence of the Institutional Mirage, the Shadow Order, and the Insecurity Triad. At the level of structural formation, Claude Ake and Franz Fanon clarify the inherited constitution of the Institutional Mirage: a postcolonial state that operates primarily as a performative and extractive apparatus, whose authority is unevenly inscribed across territorial space and sustained through symbolic rather than fully enforceable sovereignty.
At the level of mechanism, William Reno and Achille Mbembe explain the operational logic through which the Shadow Order emerges within the functional voids produced by the Mirage. Reno accounts for the relocation of authority to actors capable of enforcing compliance through control of resources and coercive capacity, while Mbembe extends this analysis by showing how coercion becomes a distributed regime of governance over life, survival, and exposure to insecurity.
At the level of persistence, Ali Mazrui and Jean-François Bayart explain why the interaction between Mirage and Shadow stabilises rather than resolves: Mazrui foregrounds the historical continuity of overlapping and non-synthesised authority systems, while Bayart highlights adaptive strategies through which elites and institutions reproduce governance through external linkage and internal accommodation. Together, these perspectives converge within the Trinity as a single analytic stack in which the Institutional Mirage, the Shadow Order, and the Insecurity Triad form a self-reproducing system of fragmented but structured sovereignty.
The Loop as System: Self-Reproduction Logic
The Insecurity Triad stabilises the system through continuous feedback:
Mirage withdraws functional void emerges;
Shadow occupies—authority substitutes
Triad institutionalises—governance stabilises;
Compliance shifts —state capacity erodes further;
Negotiation increases —dependency deepens
Loop intensifies —system reproduces.
There is no external reset mechanism within this system.
It is self-referentially stabilising under fragmentation conditions.
The Trinity of State Decay does not describe collapse. It describes a stable configuration of fragmented sovereignty sustained by asymmetry in enforcement capacity. Its resolution does not lie within the system it describes, but in the restoration of empirical sovereignty capable of reuniting legitimacy and force.
This is not the end of the argument, but the consolidation of its structure. The next and final movement will define the conditions under which the Trinity can be reversed, and the architecture of sovereignty reassembled into a single coherent system.
Trust is sacred. Stay seasoned
•Dr. Max Amuchie, CEO of Sundiata Post, is the architect of The Insecurity Triad analytical framework and the Trinity of State Decay theory. He writes The Sunday Stew, a weekly syndicated column on faith, character, and the forces that shape society, with a focus on Nigeria and Africa in a global context.
X — @MaxAmuchie | Email: [email protected] | Tel: +234(0)8053069436